Proactively Secure Your Web Applications Against Real-World Cyber Threats
Our Web Application Security Assessment Framework
A structured, standards-aligned methodology designed to identify, validate, and remediate real-world security risks.

Scope Definition & Risk Profiling
Identify applications, assets, compliance drivers, and threat models.

Architecture & Information Analysis
Review application design, authentication flows, APIs, and data paths.

Automated & Manual Reconnaissance
Run automated scanners and perform in-depth manual reconnaissance.

Exploitation & Impact Validation
Validate exploitability and demonstrate real business impact.

Risk Rating & Executive Reporting
Classify findings by business risk and compliance relevance.

Remediation Validation & Retesting
Verify fixes and confirm secure risk closure.
Your Application Is Exposed — Here’s Where Attackers Strike First
Most breaches exploit predictable weaknesses. We identify and eliminate them before they are weaponised against your business.
Enables data theft, account compromise, and regulatory violations through malicious input manipulation.
Allows credential stuffing, privilege escalation, and unauthorised system access.
Leads to leakage of PII, financial data, reputational damage, and compliance fines.
Exploitation of workflow flaws causing revenue leakage and transaction fraud.
Disrupts service availability, violates SLAs, and increases customer churn.
Systemic weaknesses across application layers that attackers routinely exploit.
OWASP-Aligned Vulnerability Coverage
 Injection & Cross-Site Scripting (XSS)
Injection & Cross-Site Scripting (XSS)
- Impact: Data theft, account compromise, regulatory penalties
- Response Input validation, query hardening, output encoding
 Authentication & Session Failures
Authentication & Session Failures
- Impact: Unauthorised access, credential abuse
- Response: MFA enforcement, session hardening, token security
 Access Control Weaknesses
Access Control Weaknesses
- Impact: Privilege escalation, data manipulation
- Response: Role validation, permission enforcement
 Insecure File Handling
Insecure File Handling
- Impact: Malware uploads, remote code execution
- Response: File validation, sandboxing, storage isolation
 Deserialization & Business Logic Flaws
Deserialization & Business Logic Flaws
- Impact: Transaction fraud, workflow abuse
- Response: Secure parsing, logic validation
 Security Misconfiguration
Security Misconfiguration
- Impact: Infrastructure exposure, data leakage
- Response: Hardening reviews, baseline enforcement
Our End-to-End Security Assessment Journey
From scoping to secure closure — a disciplined process designed for measurable risk reduction.
Risk Alignment
Define scope, compliance drivers, and threat model.
Attack Surface Mapping
Identify endpoints, APIs, and exposed assets.
Baseline Scanning
Automated scanning aligned to OWASP standards.
Manual Exploitation
Validate real-world exploitability and logic flaws.
Impact Analysis
Map findings to business and compliance risk.
Executive Reporting
Deliver actionable technical and board-level reports.
Retesting & Closure
Validate fixes and confirm secure closure.
Proven Security Engagements
Proven Security Engagements Selected anonymised case profiles demonstrating measurable risk reduction across sensitive environments.

 Financial Services — Payment Gateway
Financial Services — Payment Gateway - Environment: PCI-compliant payment platform processing 2M+ transactions/month
- Risk Identified: Authentication bypass, API abuse
- Business Impact: Regulatory exposure and fraud risk
- Outcome: Zero critical vulnerabilities after remediation

 Healthcare SaaS — Patient Portal
Healthcare SaaS — Patient Portal- Environment: Cloud-hosted patient management system
- Risk Identified: IDOR, sensitive data exposure
- Business Impact: HIPAA compliance risk
- Outcome: Secured before external audit

 E-Commerce — Enterprise Retail Platform
E-Commerce — Enterprise Retail Platform- Environment: High-volume checkout and inventory system
- Risk Identified: SQL injection, business logic flaws
- Business Impact: Revenue manipulation risk
- Outcome: 72% risk reduction in 30 days

 FinTech — Digital Lending Platform
FinTech — Digital Lending Platform- Environment: Multi-tenant lending application
- Risk Identified: Session hijacking, privilege escalation
- Business Impact: Customer account compromise risk
- Outcome: Hardened authentication and access controls
 EdTech — Learning Management System
EdTech — Learning Management System- Environment: SaaS LMS serving 500k+ user
- Risk Identified: Insecure file uploads, XSS
- Business Impact: Malware distribution exposure
- Outcome: Secure upload pipeline implemented

 Logistics — Supply Chain Platform
Logistics — Supply Chain Platform- Logistics — Supply Chain Platform
- Risk Identified: API authentication weaknesses
- Business Impact: Shipment data manipulation risk
- Outcome: API gateway security redesign

 Insurance — Claims Processing System
Insurance — Claims Processing System- Environment: Claims and policy management portal
- Risk Identified: Broken access control
- Business Impact: Data leakage and fraud risk
- Outcome: Role-based access enforcement deployed

 Manufacturing — Industrial IoT Dashboard
Manufacturing — Industrial IoT Dashboard- Environment: Cloud-connected production monitoring platform
- Risk Identified: Insecure device authentication
- Business Impact: Operational disruption risk
- Outcome: Secure certificate-based authentication introduced

 Travel & Hospitality — Booking Engine
Travel & Hospitality — Booking Engine- Environment: Online booking and payment system
- Risk Identified: Payment flow manipulation
- Business Impact: Financial loss exposure
- Outcome: Transaction validation controls implemented

 Media & Entertainment — Streaming Platform
Media & Entertainment — Streaming Platform- Environment: Subscription-based content platform
- Risk Identified: Account takeover, token reuse
- Business Impact: Revenue leakage and churn
- Outcome: MFA and token rotation enforced

 HR Tech — Employee Management System
HR Tech — Employee Management System - Environment: HRIS handling payroll and personal data
- Risk Identified: Data exposure through misconfiguration
- Business Impact: GDPR compliance risk
- Outcome: Secure configuration baseline established

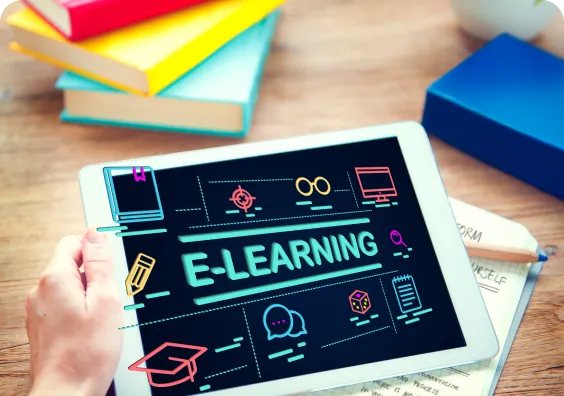
 B2B SaaS — CRM & Analytics Platform
B2B SaaS — CRM & Analytics Platform- Environment: HRIS handling payroll and personal data
- Risk Identified: Data exposure through misconfiguration
- Business Impact: GDPR compliance risk
- Outcome: Secure configuration baseline established
What we have done
Explore some of our projects showcasing our expertise in creating robust and scalable solutions.
Why Enterprises Choose Dotsquares for Application Security
A proven delivery model, certified expertise, and a governance-first approach designed for high-risk environments and compliance-driven organisations.

Proven Security Delivery
Extensive experience delivering security assessments across regulated and high-volume platforms with repeatable frameworks and accountability.

Certified & Trained Specialists
Security engineers trained in OWASP principles, CVSS-style risk scoring, and modern attack techniques relevant to real-world threats.

Manual + Automated Testing
Hybrid methodology that reduces false positives and uncovers real exploit paths, including business logic weaknesses.

Governance & Compliance Alignment
Structured reporting designed to support compliance and audit needs, aligned to frameworks such as OWASP, PCI DSS, and ISO 27001.

Actionable Remediation Support
Developer-ready remediation guidance with prioritised fixes, reproduction evidence, and optional retesting support.

Long-Term Partnership Model
Engagement models that extend beyond assessment — including retesting, optimisation, and ongoing security improvement support.
Launch a value-adding Software Integration Solutions that Drives Your Success
Connect with our experts!
Built Relationships with 15,000+ Happy Clients!
Companies employ software developers from us because we have a proven track record of delivering high-quality projects on time.

5+ Years of Average Experience

Integrity & Transparency

FREE No Obligation Quote

ISO 27001 Information Security

Outcome-Focused Approach

Transparency is Guaranteed

Focus on Security

4.8/5 Rating on Clutch

Hire a Team of Your Choice

Costs Lower Than Your Local Guy

We're here to answer all your questions.
Once you book a consultation, our experts contact you within 24 hours to discuss your needs. We define the testing scope, gather necessary information, and conduct a thorough assessment tailored to your requirements.
Our services protect your digital assets from various cyber threats, ensuring smooth operation, preventing data breaches, financial losses, and reputational damage. We identify and mitigate vulnerabilities to keep your business secure and resilient.
The assessment duration depends on your application's complexity. After an initial consultation, we provide a tailored timeline and can start assessments promptly to address any urgent security needs.
Our penetration testing is designed to minimize disruption. We operate in a controlled environment and follow strict protocols, ensuring the assessment does not impact your live systems or business operations.
Yes, we offer ongoing monitoring to identify new vulnerabilities and provide continuous support, ensuring your web application's security posture remains strong and up-to-date against emerging threats.